Table of Contents:
Envisioning Cyber Insurance in the Age of Cyber Attacks Generated by AI
In this digital age, with the rapid advance of technology, corporations are experiencing cyber-attacks with greater frequency. Given the circumstances, cyber-attacks are becoming an everyday part of business. Worse still, many of these cyber-attacks nowadays are generated by sophisticated AI models. With each attempted cyber-attack, these malicious AI models continuously train themselves to scale their capabilities to do maximum harm to companies.
Even though large chunks cyber-attacks are AI and quantum generated, most carriers are yet to update the cyber-insurance products that are capable to mitigate the risk. Given the nature of the risk, carriers need to think beyond the conventional nature of risk mitigation techniques. Traditionally, many cyber-insurance products broadly cover first party loss, third party liability, regulatory actions and incident response costs. It is also noted that unlike other insurance products, the coverage offered is tailored according to the nature of the exposure (unlike blanket coverage as in other insurance products).
AI Driven Threat Landscape: External vs. Internal Attacks
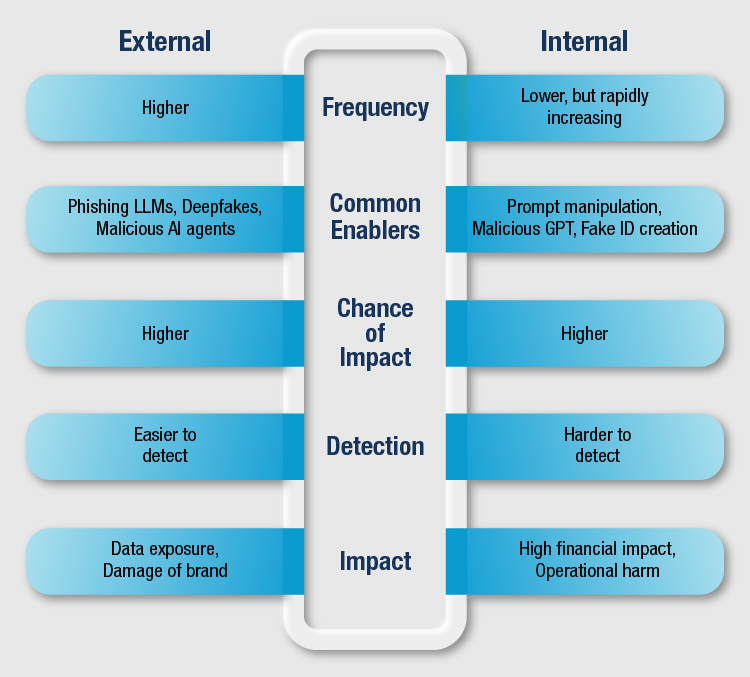
Lately it has been observed that AI-generated cyber-attacks originate both from internal as well as external sources. Even though majority of the attacks are from external sources, the attacks from internal sources are on the rise. Below is a brief comparative analysis of AI-generated external vs internal cyber-attacks.
A Layered Cybersecurity Risk Management Model
Looking at the dynamic nature of the AI-initiated cyber-attacks (both external & internal), carriers need to continuously help insureds monitor and upgrade the cyber security and threat management mechanisms. As a remedy, carriers may provide cyber insurance packaged with cyber security risk management consulting services embedded in the policy to enhance the product while countering and reducing risk. The service may be structured in three layers:
- Layer 1 – Preventative services
- Layer 2 – Infra services
- Layer 3 (Top Layer) – Cyber insurance
As AI-generated cyber-attacks get more sophisticated in nature and see an uptick in frequency, cyber security portfolios of technology companies like Mphasis empower carriers and insureds to counter AI-generated cyber-attacks by engaging them throughout the policy lifecycle.
Common Types of AI Generated Cyber Attacks
Before exploring the possibilities, let’s quickly see the most common AI-generated cyber-attacks:
- AI-generated social engineering
- Adaptive malware
- Attacks on AI systems
- AI-driven identity fraud
- Interactive and real-time manipulation
- Deepfake enabled fraud
- AI-generated cyber physical attack
- AI-generated ransomware (AI-native ransomware is still emerging. However, most ransomware attacks use AI at some stage)
Below are the common characteristics of these AI-generated cyber-attacks:
- High speed and volume
- Highly realistic and personalized
- Polymorphic and self-adaptive
- Ability to swiftly detect vulnerabilities
- Real-time adaptation to each defender’s response
- Use of open-source AI models
- Ability of autonomous navigation through complex industrial networks
Mphasis offers opportunities to partner with the carriers in the below areas:
- Continuous underwriting – Involves continuous risk assessment (Preventative services)
- Continuous monitoring of the insured’s cyber security ecosystem (Preventative & Infra services)
- Investigation during claim payout (Cyber Insurance)
- AI driven cyber insurance control framework (Infra Services)
The Process of Continuous Underwriting & Risk Assessment
While it is obvious that carriers define very robust underwriting guidelines, they may fall short of technical expertise to perform the end-to-end activities. Mphasis’ proven capabilities effectively manage the underwriting process and risk assessment (not exhaustive):
- Assist in defining comprehensive underwriting scoring mechanism:
- Use No-code platforms like Tines to auto-generate questionnaires from threat intelligence to better assess the risk and insured event preparedness
- Use AI agents to continuously probe insureds systems and perform continuous monitoring to scale underwriting best practices and workflow
- Update the underwriting guidelines frequently and on a random basis
While the carriers have the ability to update the underwriting guidelines, Mphasis helps them gauge the risk posed by the ever-evolving malicious AI models to further refine appetite and pricing. This in turn will help carriers to continuously update underwriting guidelines effectively.
- Mandatory compliance with local Data Protection guidelines
Before offering coverage, carriers need to verify if the insured is compliant with the local Data Protection (DP) regulations. Leveraging Mphasis’ expertise, the carrier can ensure that insured comply with the DP regulations before offering any coverage and limit the exposure of future regulatory action if there is an event.
- Decentralized information exchange among carriers
Cyberattacks represent a systemic risk impacting individuals, enterprises, and carriers alike. Addressing this challenge requires a collaborative, ecosystem-wide approach rather than isolated efforts. Mphasis can help create a blockchain-enabled information-sharing framework that will assist carriers collectively strengthen cyber resilience through the following measures:
- Sharing underwriting guidelines amongst carriers where permissible
- Sharing any new incident details amongst carriers
- Sharing cybersecurity-related AI model parameters across carriers – Proprietary, sharing model parameters will help carriers develop and train the models faster and more efficiently.
Monitoring the Insured’s Cyber Security Ecosystem
AI-generated cyberattacks increasingly target access management layers as the primary point of attack. Carriers and enterprises must therefore enforce continuous monitoring of access credential analytics to detect and remediate anomalies in real time. Mandatory multi-factor authentication (MFA) helps resist AI-driven phishing and credential abuse, while implementing a zero-trust architecture ensures that no user or system is trusted by default, significantly reducing lateral movement and attack impact.
- Advanced Email, Messaging & Deepfake Protection as a Countermeasure
AI-generated cyberattacks heavily rely on phishing, impersonation and synthetic media to bypass human judgment. AI-based phishing detection helps counter these attacks by identifying anomalous language patterns, sender behavior and intent in real time. Video and voice deepfake detection mitigate executive impersonation and social engineering fraud driven by generative AI. Additionally, automatic flagging of emails and messages requesting payments or sensitive actions introduces a critical friction point, significantly reducing the success rate of AI-enabled financial fraud and business email compromise.
- AI-Powered Threat Detection and Response
AI-generated cyberattacks evolve rapidly and often evade traditional, rule-based security controls:
- AI-driven threat detection, such as UEBA with machine learning based anomaly detection, enables early identification of abnormal user and system behavior.
- Coupled with automated response mechanisms through SOAR platforms (e.g., Palo Alto Cortex), organizations can contain and remediate threats in near real time, significantly reducing dwell time and attack impact
- Continuous Vulnerability Detection
AI-driven attacks rapidly exploit exposed and misconfigured assets, making continuous vulnerability detection essential. API security monitoring, automated attack surface management and risk-based patching help identify and prioritize exploitable weaknesses in real time. Software supply chain scanning (SBOM) further reduces exposure by detecting hidden vulnerabilities in third-party components before they are weaponized by malicious AI.
- Data Protection & Ransomware Prevention
AI-enabled ransomware targets high value data through automation and precision. Strong data classification, encryption, immutable backups and real-time behavioral monitoring help prevent data exfiltration and limit blast radius. These controls reduce both operational disruption and insured’s loss severity.
As organizations increasingly deploy AI systems, these tools themselves become high value targets. Protecting AI models, training data and inference pipelines through access controls, monitoring and integrity checks. This prevents model poisoning, data leakage and adversarial manipulation by malicious AI.
Effective governance ensures that technical defenses evolve alongside AI-driven threats. Clearly defined security policies, continuous compliance monitoring and board-level oversight enable consistent enforcement of controls. Strong governance also aligns cybersecurity posture with underwriting requirements and regulatory expectations.
Thorough Investigation of Claims Arising Due to AI-Generated Cyber-Attack
Once a claim occurs due to AI-generated cyber-attack, it might be difficult for carriers to investigate the claim due to the technical nature of the attack. Below is a high level structure of the investigation:
- Verification of As-Is cyber security measures
Mphasis will help the carrier assess the insureds’ cyber security measures before and during the time of the attack. Some of the verifications would include (not limited to) the below:
- Evaluate the MFA and VPN exposure
- Verify compliance with DP regulations
- Verify compliance with carrier’s underwriting guidelines, as well as policy provisions
- Investigation of the nature of attack
Mphasis will be instrumental in determining if the attack was caused by any AI model. Subsequently, Mphasis will also help in determining the impact of the attack. This process will enable the carrier to determine how the attack originated and if it took place even after complying with the protocols
- Determining the lapses and immediate controls that need to be implemented
Lastly, Mphasis will be able to determine the lapses (if any) in the insured ecosystem. Subsequently, it will help determine if the breach happened due to the lapse
Mphasis AI-Driven Cyber Insurance Control Framework:
Assess: Continuously evaluate the insured’s cyber posture, attack surface and AI exposure using real-time data; this supports dynamic Underwriting, Risk scoring, Pricing, etc.
Prevent: Implement and enforce preventive controls such as zero trust, strong identity access management, secure AI systems and regulatory compliance. This reduces attack success probability
Detect: Leverage AI-Driven Monitoring to identify anomalous behavior, phishing, deepfakes and adaptive attacks in near real time and focus on early detection significantly
Respond: Automate containment and remediation while enabling AI-assisted forensics. This ensures faster recovery and accurate claims adjudication
Building Robust Cyber Defense and Risk Transfer Mechanisms
AI-generated cyberattacks are not merely escalating risk; they are redefining the very architecture of cyber insurance. In this new reality, static policies, episodic underwriting and reactive claims handling are becoming relics of a bygone era. The future belongs to a living insurance model, one anchored in continuous engagement, real-time intelligence and collaboration between carriers, insureds and technology partners.
By fusing carrier’s acumen with Mphasis’ advanced AI, cyber security services and digital engineering capabilities, carriers can transcend passive risk transfer and evolve into agents of active risk reduction, building a Cyber Insurance ecosystem that is resilient by design, adaptive by nature and economically aligned for the age of artificial intelligence.
This Blog is Written by:
Shouvik Lahiri - Senior Principal Consultant, Insurance
Saikrishna B - Associate Vice President, Insurance